Learn Ethical Hacking From A To Z Beginner To Expert Course




Course Overview:
Welcome to Course Plus! This comprehensive course on ethical hacking will take you on a journey from the basics to advanced techniques. You’ll learn how to secure systems, understand hacker methodologies, and protect against cyber threats. With modules ranging from networking basics to mobile hacking and branding yourself as an ethical hacker, this course covers everything you need to excel in cybersecurity. Gain hands-on experience through lab setups, real-world scenarios, and interactive exercises. Whether you’re a beginner or looking to enhance your skills, this course provides practical knowledge and career guidance to help you thrive in this growing field.
Why Enroll in this Course?
Start the Learn Ethical Hacking From A-Z course on Course Plus to gain the essential skills needed to navigate the fast-evolving world of cybersecurity. This course is perfect for both beginners and professionals aiming to upskill, offering step-by-step guidance in penetration testing, WiFi hacking, cryptography, and more. With hands-on labs and practical tools like Kali Linux, you’ll master real-world hacking scenarios while staying compliant with ethical standards. Discover the latest cybersecurity trends, job opportunities, and earning potential in the UK and beyond. This course is not just about learning skills—it’s about launching your ethical hacking career with confidence.
Investment Value:
- Lifetime access to a comprehensive ethical hacking curriculum.
- Practical, hands-on training with industry-standard tools like Kali Linux.
- Career-focused guidance on freelancing, consulting, and client acquisition.
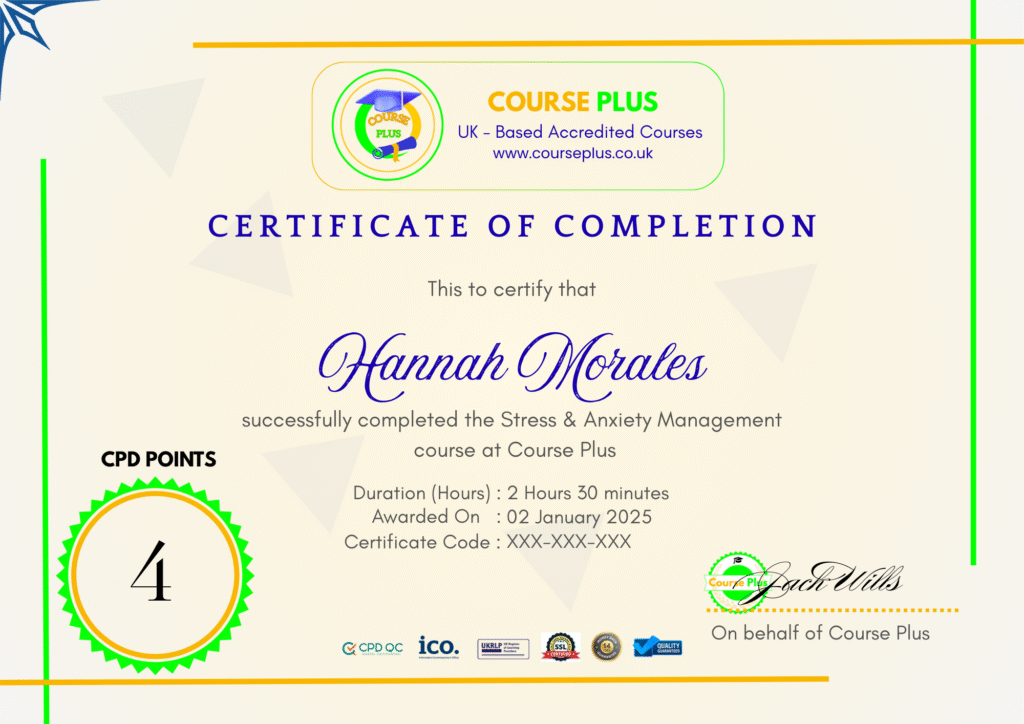
- Certification of completion to showcase your skills to employers.
- Access to community forums for networking and ongoing support.
Technical Specifications:
- Duration: Self-paced, approximately 14+ hours of video content.
- Requirements: Internet connection, PC or Mac, and access to Virtual Machine software.
- Support: Lifetime updates and access to an instructor Q&A forum.
- Format: Video lectures.
Learning Outcome
- Understand the basics of networking, IP protocols, and subnets.
- Learn ethical hacking techniques, tools, and methodologies.
- Set up and configure a secure hacking lab environment.
- Conduct WiFi penetration testing and information gathering.
- Master Linux, Python, Bash scripting, and PowerShell basics.
- Perform reconnaissance, analyze vulnerabilities, and launch exploits.
- Secure web applications through SQL injection and brute force prevention.
- Understand mobile hacking techniques and data security practices.
- Build your personal brand and start a career as an ethical hacker.
- Stay anonymous online using VPNs, TOR browsers, and other tools.
Conclusion
Embark on your journey to becoming a cybersecurity expert with Course Plus! The Learn Ethical Hacking From A-Z course is your gateway to mastering the skills needed to secure systems and protect against threats. With expert guidance, practical labs, and career-focused insights, you’ll gain the confidence to excel in this high-demand field. Enroll today and take the first step toward a rewarding career in ethical hacking.
Next Steps:
- Register on Course Plus platform
- Access course materials
- Join community discussions
- Earn certification
Course Curriculum
Course Introduction
-
Course Overview
09:00 -
About Your Instructors
03:00 -
Section Overview
04:00 -
Current Cybersecurity Market
09:00 -
The 3 Types of Hackers
05:00 -
The 4 Elements of Security
05:00 -
Ethical Hacking Terminology
04:00 -
Common Methods of Hacking
08:00 -
Cyber Security and Ethical Hacking Overview
03:00 -
Ethical Hacking vs Pentration Testing
06:00 -
Jobs Opportunities in Cybersecurity
02:00 -
Who’s This Course For
02:00
Networking Basics
-
Networking Section Overview
12:00 -
How Data Travels Across The Internet
02:00 -
Understanding Ports and Protocols
09:00 -
Public and Private IP Address Overview
03:00 -
What Are Subnets
03:00 -
The Average Network vs Remote Based
06:00
Setting Up Your Hacking Lab
-
Hacking Lab Section Overview
09:00 -
Understanding Virtual Machines
04:00 -
Setup Your Kali Linux Machine
10:00 -
VN Setup and Testing Vulnerable Systems
24:00
Linux/Python/Bash & PowerShell Basics
-
Linux+Python+Bash+Powershell Basics Overview
06:00 -
Linux Basics
11:00 -
Working With Directories and Moving Files
03:00 -
Installing and Updating App Files
03:00 -
Linux Text Editors
05:00 -
Searching For Files
03:00 -
Bash Scripting
10:00 -
Python Basics
11:00
How To Remain Anonymous On The Web
-
Remaining Anonymous Section Overview
07:00 -
TOR Browser Overview
06:00 -
Anonsurf Overview
04:00 -
Changing Mac Addresses
03:00 -
Using a Virtual Private Network and Server (VPN, VPS)
05:00
How To Hack Into WIFI
-
WiFi Hacking Section Overview
06:00 -
Wifi Hacking System Setup
10:00 -
WEP Hacking Attack #1
09:00 -
WEP Hacking Attack #2
05:00 -
WPA and WPA2 Hacking
11:00
Passive & Active Reconnaissance (Information Gathering)
-
Reconnaissance Section Overview
04:00 -
Passive + Active Recon
02:00 -
Recon-ng Overview
15:00 -
Whois Enum
02:00 -
DNS Enumeration Overview
03:00 -
Netcraft DNS Information
03:00 -
Google Hacking Overview
05:00 -
Shodanio Overview
03:00 -
Securityheaderscom (Analyze HTTPS Headers of website)
02:00 -
Ssllabscomssltest (Look for SSL issues on website)
03:00 -
Pastebincom (Sensitive Information)
01:00 -
NMAP Port Scanning (Discover open ports, OS, Services,
16:00 -
Netcat Overview + SMB _ NFS Enumeration
15:00 -
Nikto and Sparta Web Application Scanner
06:00 -
SMPT Enumeration + Nessus +Openvas Scanners
05:00
Launching Attacks
-
Launching Attacks Overview
11:00 -
Analyzing Information Gathered
04:00 -
Taking Advantage of Telenet
07:00 -
Searching and Understanding Exploits
06:00 -
Copy Exploits From Searchsploit
03:00 -
Understanding Exploits
05:00 -
Launching Exploits
25:00 -
Brute Force Attacks
07:00 -
How To Crack Passwords
05:00 -
ARP Spoofing Overview
22:00 -
Introduction To Cryptography
14:00
Post Exploitation
-
Post Exploitation Section Overview
04:00 -
Privledge Escalation
30:00 -
Transferring Files Within Victim, Creating Custom Malware +Evading AV
28:00 -
Installing a Keylogger
03:00 -
Installing a Backdoor
07:00
Website & Web Application Hacking
-
Website and Web App Hacking Overview
07:00 -
Web Application Scanning
08:00 -
Directory Buster Hacking Tool
03:00 -
Nikto Web App Hacking Tool
04:00 -
SQLmap and SQL Ninja Overview
01:00 -
How To Execute Brute Force Attacks
14:00 -
Using Command Injection
04:00 -
Malicious File Uploads
11:00 -
Local and Remote File Inclusion
11:00 -
SQL Injection
19:00 -
Using Cross Site Forgery
11:00 -
Cross Site Scripting Overview
13:00
Mobile Phone Hacking & Security
-
Mobile Phone Hacking Section Overview
11:00 -
Mobile Attack Vectors
02:00 -
Mobile Hacking with URLs
03:00 -
Jail Breaking and Rooting Considerations
01:00 -
Privacy Issues (Geo Location)
01:00 -
Mobile Phone Data Security
03:00
Getting Your Name Out There As An Ethical Hacker
-
Getting Your Name Out There Section Overview
03:00 -
Building A Brand
10:00 -
Personal Branding
14:00 -
Setup Your Website and Blog
12:00 -
Writing a Book
10:00 -
Starting a Podcast
09:00 -
Networking Overview
07:00
How To Make Money As An Ethical Hacker
-
Making Money Section Overview
02:00 -
Bug Bounty Programs
05:00 -
How To Start Freelancing
11:00 -
How To Start Client Consulting
10:00
How To Start A Career In Cybersecurity
-
Potential Salary and Cybersecurity Roadmap
11:00 -
Book Recomendations
03:00 -
Places to Practice Hacking for Free
04:00 -
Taking Advantage of Telenet
07:00
Student Ratings & Reviews

-
LevelExpert
-
Duration12 hours 51 minutes
-
Last UpdatedSeptember 30, 2025
A course by
Material Includes
- 24/7 Support
- Online e-learning platform
- Interactive modules
- Video-based instruction
- Practical exercises
- Certification (on demand)
- Assessment on demand
Requirements
- Minimum age: 18 years
- Access to a computer with internet
- Willingness to learn and engage
Target Audience
- Professionals looking to transition into cybersecurity.
- IT and network administrators seeking to secure their systems.
- Students and beginners aspiring to become ethical hackers.
- Freelancers and consultants aiming to offer cybersecurity services.
- Tech enthusiasts interested in understanding hacking and cyber defense.
- Anyone passionate about building a career in ethical hacking.